An HF NFC/RFID reader or coupler usually spends most of its operating time waiting for a contactless card to arrive.
To detect this arrival, the reader or coupler must
- ensure continuous or quasi-continuous transmission of its carrier, since it is its own RF field (magnetic waves) that remotely powers the card,
- send search frames in an un-interrupted loop, using all the protocols it supports (REQA/WUPA, REQB/WUPB, Anticall, SENS_REQ, etc), to give the card the opportunity to respond as soon as it has been powered-up.
Obviously, this means that most of the operating time consists of… wasting a lot of energy, just to wait.
The Tartar Steppe (Il deserto dei Tartari) is a novel by Dino Buzzati, that tells the story of an officer, who spends all his energy waiting for the arrival of a contactless card. Well, not exactly, but, you’ve got the idea.
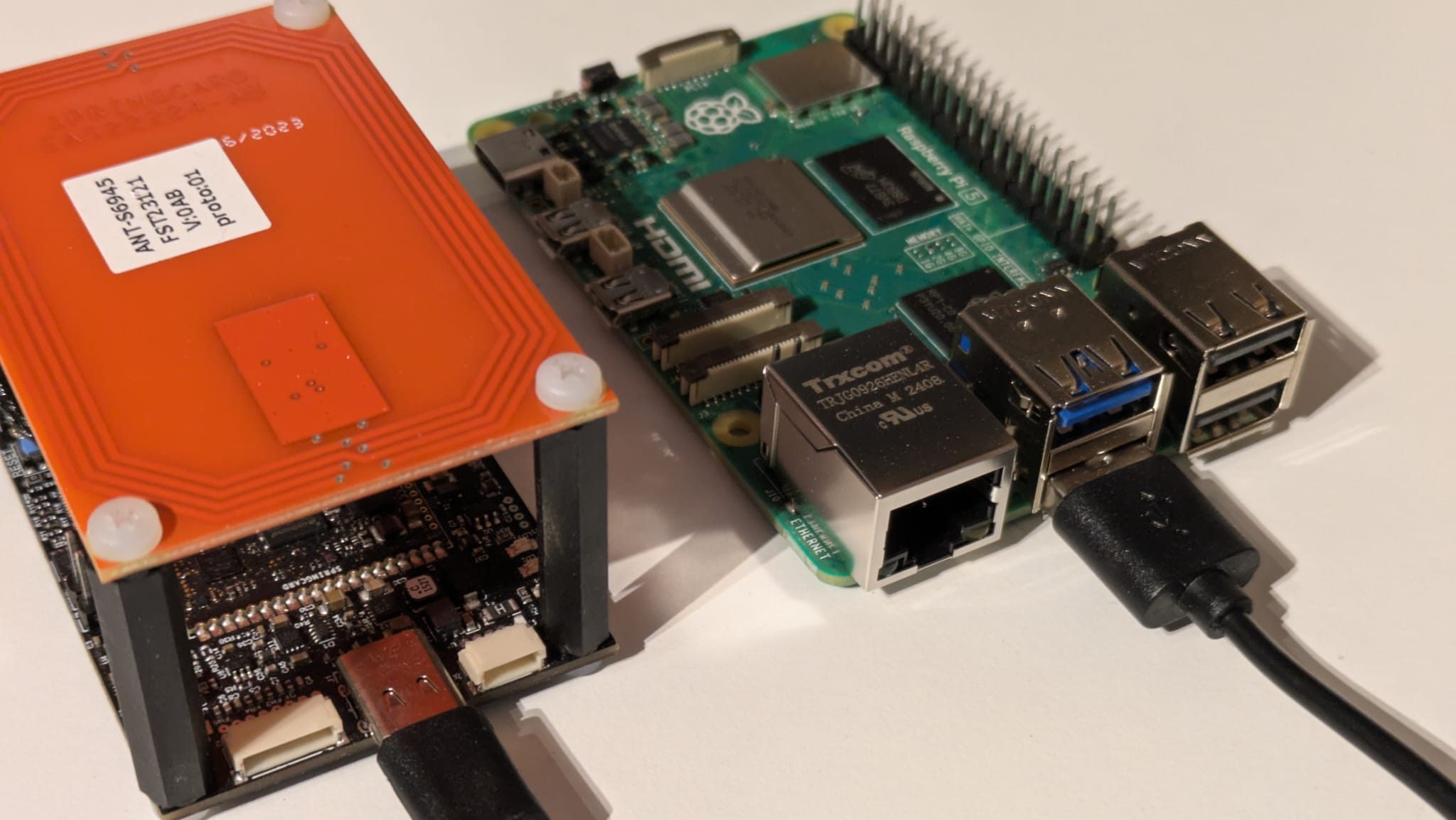
In the SpringSeed M519 module, and also in most other SpringCore products, the card waiting policy (polling policy) can be optimised to reduce the average power consumption of the product.
In highly demanding use cases, the LPCD (low-power card detection) feature can even dramatically reduce standby power requirement, to less than 10mA (however, this comes at the price of some implementation constraints, which you must be aware of before using this mode).