The rfidscan-tool command line
The rfidscan-tool command line application is available for any OS that supports libusb, HID-API or hidraw.
We’ve tested it on:
- Windows XP / Vista / 7 / 8
Mac OS X- Linux (Ubuntu, Debian, etc)
- Raspberry Pi (on Raspbian distro)
rfidscan-tool has been inspired by blink1-tool, the command-line application that controls the blink(1) USB notification light. Most of the source code comes from this application. and therefore we use the same licence model.
Note for Mac OS X: currently the tool is able to send commands to the RFID Scanner, but fails to receive its response (IOHIDDeviceGetReport always returns a timeout error — without waiting). This issue is under investigation.
Binary download
To get rfidscan-tool for your machine, visit our github releases page, and search for a version supported by your OS / target CPU.
Here’s 4 direct links to the first public version (v14.11):
- Windows (you’ll need the Visual C++ 2010 Redistributable Package to run this application)
Mac OS X- Linux (x86 PC)
- Raspberry Pi
Source code download
To compile your own version of rfidscan-tool, just checkout the rfidscan project from github and compile the rfidscan-tool subproject. Something like the below will work 99% of the time:
# git clone https://github.com/springcard/rfidscan-tool.git
# cd rfidscan-tool
# make
For a Windows target, we provide .SLN projects to be opened with the (free of charge) Microsoft Visual C++ 2010 Express IDE.
Usage
On Windows, you may invoke the binary from any command line box without restriction.
On MacOS X and on most versions of Linux (including on Raspberry Pi), you will need to either run as root (sudo rfidscan-tool <...>) or install udev rules as described in https://github.com/springcard/rfidscan-tool/blob/master/51-rfidscan.rules.
When running rfidscan-tool without any argument, it will print a help page like the one below.
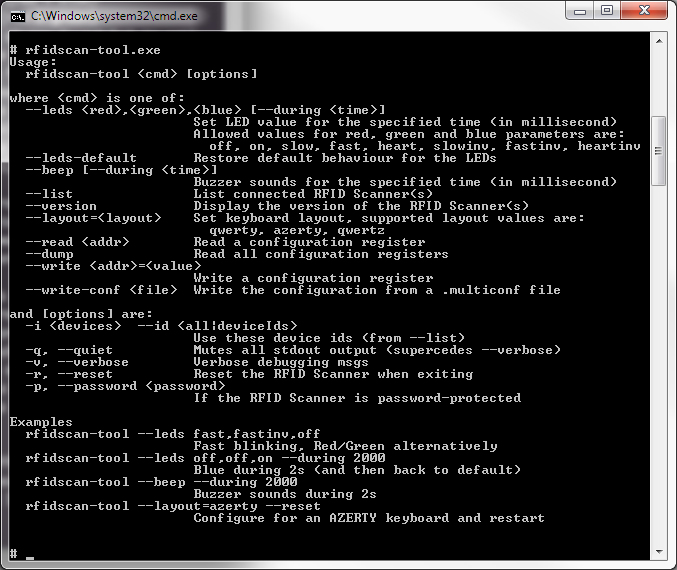
Here’s the detail of all commands:
rfidscan-tool <cmd> [options]
rfidscan-tool ––list
List all connected RFID Scanners.
rfidscan-tool ––version
Show the RFID Scanner’s firmware version.
rfidscan-tool ––test
Perform a routine test on the RFID Scanner(s).
rfidscan-tool ––leds <red>,<green>,<blue> [–during <time_ms>]
Drive the RFID Scanner’s LEDs. Allowed values for the red, green and blue parameters are
off: the LED is switched OFFon: the LED is switched ONslow: slow blinkingfast: fast blinkingheart: “heart beat”slowinv: slow blinking, invertedfastinv: fast blinking, invertedheartinv: “heart beat”, inverted
The during parameter is optionnal ans specify how long (in milliseconds) the specified value remains active, before the RFID Scanner goes back to the default sequence.
If this parameter is missing, the LED command lasts forever (at least until another LED command is issued).
rfidscan-tool ––leds-default
Let the RFID Scanner drives its LEDs itself as usual.
rfidscan-tool ––beep [––during <time_ms>]
Switch ON the RFID Scanner’s buzzer for the specified time (in milliseconds).
rfidscan-tool ––read <addr>
Read the configuration register at the specified address.
rfidscan-tool ––write <addr>=<value>
Write the specified value into the configuration register at the specified address. Leavevalue empty to erase the register.
rfidscan-tool ––dump
Dump all the configuration registers.
Note: the “sensitive” registers (keys for the Master Card and password) are hidden by “XX” chars.
rfidscan-tool ––write-conf <filename>
Write the configuration registers from the specified file (use a file produced by MultiConf software).
Usage options
Values for [options] are
-d <device num> --devices <device num>: perform the command only to this device (from--list), default is all devices (same as-d all)-q --quiet: suppress most output messages-v --verbose: verbose debugging messages-r --reset: reset the RFID Scanner (to apply the new configuration)-p --password <password>: to access a RFID Scanner that is password-protected
Other tool
On this page you will find a Python script used to control the LEDs and Buzzer of a Prox’N’Roll (thanks Armel Esnault)